net
Root Servers
Network Clock Synchornization
cable data transfer
- data (assuming both sides of pc have same clock rate, ie: synchroized clock - GPS/Antenna)
- data (atomic clock in the computer itself) (uncommon)
- data & clock (two pair of wires) (short distance)
- data (manchester coding) (common)
Network framing
HDLC: High level data-link control
0111 1110is also the frame delimeter (Flag)0111 11010bit stuffingEthernet frame bytes usually range from 64 ~ 1500 ~ 9600
- Inter-frame gap (IFG) (Silence waves)
- Preamble (56 bits
1010 1010* 7) (distinct pattern waves synchorizing its clock) - Start of frame delimeter
1010 1011 - data follows the delimeter
Ethernet (MAC Address)
- Preamble
10101010*7 - SFD
1010 1011 - Destination Address (6 bytes)
- Source Address (6 bytes)
- Ether Type (2 byte) IP | other
- Payload (46 ~ 1500 ~ 9000 bytes)
- Frame Check Sequenc (4 bytes) an alogrithm calc from Destination address to end of payload
PPP (Point to Point)
- Flag
0111 1110 - Address (1 byte) ff (hex)
- Control (1 byte) 03 (hex)
- Protocol (2 bytes)
- Payload (40 ~ 1500 bytes)
- FCS (4 bytes)
- Flag
0111 1110
Internet Protocol (IP)
- Version (4 bytes)
- IHL, Internet Header Length (4 bytes)
- Type of Service (8 byets)
- Total Length (16 bytes)
- Identification (16 bytes)
- Flags
- Fragment Offset
- Time to Live (8 bytes), initial value 255
- Protocol (8 bytes)
- Header Checksum (16 bytes), checksum on header, not payload
- Source Address (32 bytes)
- Destination Address (32 bytes)
- Options (rare to see, Example: timestamp, record route, source route)
- Padding (rare to see)
Example Internet Datagram Header
0 1 2 3
0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
|Version| IHL |Type of Service| Total Length |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Identification |Flags| Fragment Offset |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Time to Live | Protocol | Header Checksum |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Source Address |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Destination Address |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Options | Padding |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
IP Packet fragments and reassembly
- MTU Maximum Transimission Unit
- Largest IP packet a network will handle
- Arriving IP packet maybe larger (Max IP packet size = 65535 bytes)
- Sender or router will split the packet into multiple fragments
- Destination will reassemble the packet
- IP header fields(Identification/Flags/Fragment Offset) used to identify and order related fragments
- All fragments of a single datagram have the same identification number
- Flag: 1st bit, reserved must be zero; 2nd bit, DF -- do not fragment; 3rd bit, MF -- more fragment
- Fragment offset: 1st fragment has offset = 0
Address Resolution Protocol (ARP)
- HW Address type
- Protocol Address Type
- HW Address Length
- Protocol Address Length
- OP Code
- Hardware Address of Sender
- Protocol Address of Sender
- Hardware Address of Target
- Protocol Address of Target
Internet Control Message Protocol (ICMP)
headers differ a little bit from ICMP type to ICMP type. Most of the ICMP types are possible to group by their headers.
- Type (8 bits)
0Echo Reply3Destination Unreachable4Source Quench5Redirect8Echo11Time Exceeded12Parameter Problem13Timestamp14Timestamp Reply15Information Request16Information Reply
- Code (8 bits) depends on Type above
- Checksum (16 bits)
- Identifier
- Sequence Number
- data...
Transmission Control Protocol (TCP)
- Source Port (16 bits)
- Destination Port (16 bits)
- Sequence Number (32 bits)
- Acknowledgment Number (32 bits)
- Data Offset (4 bits)
- Reserved (6 bits)
- Control Bits: 6 bits (from left to right):
- URG: Urgent Pointer field significant
- ACK: Acknowledgment field significant
- PSH: Push Function
- RST: Reset the connection
- SYN: Synchronize sequence numbers
- FIN: No more data from sender
- Window (16 bits), for reciver end
- Checksum (16 bits)
- Urgent Pointer (16 bits, Example: Maxiumum segment size, window scale, timestamp)
- Options (variable)
- Padding
- data
TCP Header Format
0 1 2 3
0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Source Port | Destination Port |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Sequence Number |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Acknowledgment Number |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Data | |U|A|P|R|S|F| |
| Offset| Reserved |R|C|S|S|Y|I| Window |
| | |G|K|H|T|N|N| |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Checksum | Urgent Pointer |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Options | Padding |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| data |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
TCP Connection State Diagram
+---------+ ---------\ active OPEN
| CLOSED | \ -----------
+---------+<---------\ \ create TCB
| ^ \ \ snd SYN
passive OPEN | | CLOSE \ \
------------ | | ---------- \ \
create TCB | | delete TCB \ \
V | \ \
+---------+ CLOSE | \
| LISTEN | ---------- | |
+---------+ delete TCB | |
rcv SYN | | SEND | |
----------- | | ------- | V
+---------+ snd SYN,ACK / \ snd SYN +---------+
| |<----------------- ------------------>| |
| SYN | rcv SYN | SYN |
| RCVD |<-----------------------------------------------| SENT |
| | snd ACK | |
| |------------------ -------------------| |
+---------+ rcv ACK of SYN \ / rcv SYN,ACK +---------+
| -------------- | | -----------
| x | | snd ACK
| V V
| CLOSE +---------+
| ------- | ESTAB |
| snd FIN +---------+
| CLOSE | | rcv FIN
V ------- | | -------
+---------+ snd FIN / \ snd ACK +---------+
| FIN |<----------------- ------------------>| CLOSE |
| WAIT-1 |------------------ | WAIT |
+---------+ rcv FIN \ +---------+
| rcv ACK of FIN ------- | CLOSE |
| -------------- snd ACK | ------- |
V x V snd FIN V
+---------+ +---------+ +---------+
|FINWAIT-2| | CLOSING | | LAST-ACK|
+---------+ +---------+ +---------+
| rcv ACK of FIN | rcv ACK of FIN |
| rcv FIN -------------- | Timeout=2MSL -------------- |
| ------- x V ------------ x V
\ snd ACK +---------+delete TCB +---------+
------------------------>|TIME WAIT|------------------>| CLOSED |
+---------+ +---------+
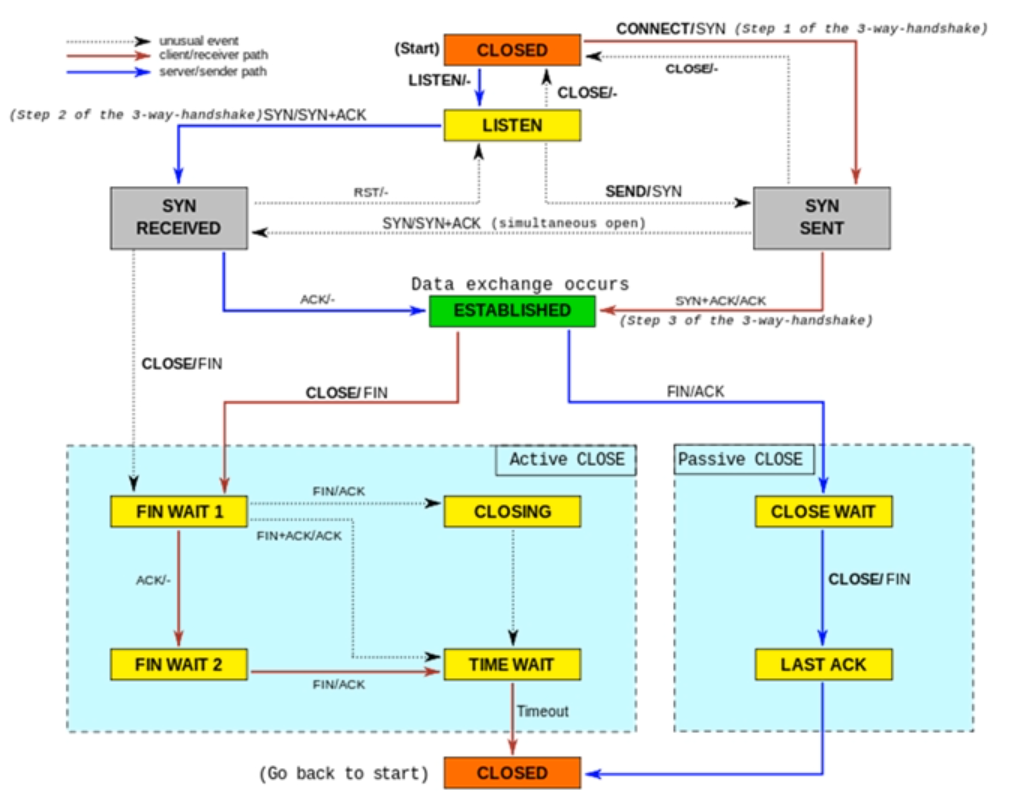
TCP Connection Internal states
| State | Timeout value |
|---|---|
| NONE | 30 minutes |
| ESTABLISHED | 5 days |
| SYN_SENT | 2 minutes |
| SYN_RECV | 60 seconds |
| FIN_WAIT | 2 minutes |
| TIME_WAIT | 2 minutes |
| CLOSE | 10 seconds |
| CLOSE_WAIT | 12 hours |
| LAST_ACK | 30 seconds |
| LISTEN | 2 minutes |
- LISTEN (SERVER) represents waiting for a connection request from any remote TCP and port
- SYN-SENT (CLIENT) represents waiting for a matching connection request after ahving sent a connection request
- SYN-RECEIVED (SERVER) represents waiting for a confirming connnection request acknowledgement after having both received and sent a connection request
- ESTABLISHED (both SERVER and CLIENT) represents an open connection, data received can be delivered to the user. The normal state for the data transfer phase of the connection
- FIN-WAIT-1 (both SERVER and CLIENT) represents waiting for a connection termination request form the remote TCP, or an acknowledgment of the connection termination request previously sent.
- FIN-WAIT-2 (both SERVER and CLIENT) represents waiting for a connection termination request from the remote TCP
- CLOSE-WAIT (both SERVER and CLIENT) represents waiting for a connection termination request from the local user.
- CLOSING (both SERVER and CLIENT) reqpresents waiting for a conenction termination request acknowledgment form the remote TCP.
- LAST-ACK (both SERVER and CLIENT) represents waiting for an acknowledgment of the connnection termination request previously sent to the remote TCP (which includes an acknowledgment of its connenction termination request)
- TIME-WAIT (either SERVER or CLIENT) represents waiting for enough time to pass to be sure the remote TCP received the acknowledgment of its connection termination request
- CLOSED (both SERVER and CLIENT) represents no connection state at all
User Datagram Protocol (UDP)
User Datagram Header Format
0 7 8 15 16 23 24 31
+--------+--------+--------+--------+
| Source | Destination |
| Port | Port |
+--------+--------+--------+--------+
| | |
| Length | Checksum |
+--------+--------+--------+--------+
|
| data octets ...
+---------------- ...
Stream Control Transmission Protocol (SCTP)
SCTP Common Header Format
0 1 2 3
0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Source Port Number | Destination Port Number |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Verification Tag |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
| Checksum |
+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
Gateway to Gateway Protocol (GGP)
Network Related Commands
sudo lshw -class networkDisplay network related driver details & capabilities
*-network
description: Ethernet controller
product: Virtio network device
vendor: Red Hat, Inc.
physical id: 3
bus info: pci@0000:00:03.0
version: 00
width: 32 bits
clock: 33MHz
capabilities: msix bus_master cap_list rom
configuration: driver=virtio-pci latency=0
resources: irq:10 ioport:c000(size=64) memory:febd1000-febd1fff memory:feb80000-febbffff
*-virtio0
description: Ethernet interface
physical id: 0
bus info: virtio@0
logical name: eth0
serial: 00:16:3e:xx:xx:32
capabilities: ethernet physical
configuration: autonegotiation=off broadcast=yes driver=virtio_net driverversion=1.0.0 ip=172.19.177.182 link=yes multicast=yes
*-network:0
description: Ethernet interface
physical id: 1
logical name: vetha1730ca
serial: be:xx:xx:xx:xx:95
size: 10Gbit/s
capabilities: ethernet physical
configuration: autonegotiation=off broadcast=yes driver=veth driverversion=1.0 duplex=full link=yes multicast=yes port=twisted pair speed=10Gbit/s
*-network:1
description: Ethernet interface
physical id: 2
logical name: veth327dd01
serial: 36:3a:c9:7e:eb:a1
size: 10Gbit/s
capabilities: ethernet physical
configuration: autonegotiation=off broadcast=yes driver=veth driverversion=1.0 duplex=full link=yes multicast=yes port=twisted pair speed=10Gbit/s
ifconfig -aDisplay and manipulate route and network interfaces
# ifconfig command to disable a network interface
sudo ifconfig [Interface name] down
sudo ifconfig [Interface name] up
# ip command to disable a network interface
sudo ip link set [Interface name] down
sudo ip link set [Interface name] up
br-83bbca862df5: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.16.8.1 netmask 255.255.255.0 broadcast 172.16.8.255
ether 02:42:49:e5:93:fc txqueuelen 0 (Ethernet)
RX packets 289128 bytes 76563100 (76.5 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 280438 bytes 43653997 (43.6 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
docker0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
inet 172.17.0.1 netmask 255.255.0.0 broadcast 172.17.255.255
ether 02:42:cf:28:a7:14 txqueuelen 0 (Ethernet)
RX packets 54890 bytes 4890067 (4.8 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 68300 bytes 158770619 (158.7 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
eno1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.1.78 netmask 255.255.255.0 broadcast 192.168.1.255
inet6 240e:388:6252:300:7d55:a501:a0ad:7bc9 prefixlen 64 scopeid 0x0<global>
inet6 fe80::ff3f:37a3:60ba:8d37 prefixlen 64 scopeid 0x20<link>
inet6 240e:388:6252:300:e5e6:1980:c300:527c prefixlen 64 scopeid 0x0<global>
ether 54:b2:03:98:55:1e txqueuelen 1000 (Ethernet)
RX packets 513816 bytes 283987872 (283.9 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 421736 bytes 121870605 (121.8 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
device interrupt 16 memory 0xdc300000-dc320000
enp5s0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
ether 54:b2:03:98:40:1f txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
device memory 0xdc200000-dc21ffff
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
loop txqueuelen 1000 (Local Loopback)
RX packets 3470657 bytes 1239570393 (1.2 GB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 3470657 bytes 1239570393 (1.2 GB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
tun0: flags=4305<UP,POINTOPOINT,RUNNING,NOARP,MULTICAST> mtu 1500
inet 10.8.0.2 netmask 255.255.255.0 destination 10.8.0.2
inet6 fe80::58ab:c6c4:942f:9b9c prefixlen 64 scopeid 0x20<link>
unspec 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00 txqueuelen 500 (UNSPEC)
RX packets 33171 bytes 24646151 (24.6 MB)
RX errors 0 dropped 24 overruns 0 frame 0
TX packets 28739 bytes 7590120 (7.5 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
veth08294be: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
ether e2:a3:3b:22:be:5d txqueuelen 0 (Ethernet)
RX packets 13397 bytes 7111626 (7.1 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 15875 bytes 1439441 (1.4 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
veth102727a: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
ether 8e:19:46:b9:1a:c1 txqueuelen 0 (Ethernet)
RX packets 215280 bytes 19914918 (19.9 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 185571 bytes 30306107 (30.3 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
vethf386f6e: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
ether c2:26:6d:c9:f6:3a txqueuelen 0 (Ethernet)
RX packets 395348 bytes 72958846 (72.9 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 367646 bytes 72094363 (72.0 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
wlp6s0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.2.55 netmask 255.255.255.0 broadcast 192.168.2.255
inet6 fe80::e846:f0c7:6ed0:80a1 prefixlen 64 scopeid 0x20<link>
ether 40:ec:99:48:94:77 txqueuelen 1000 (Ethernet)
RX packets 272418 bytes 269750582 (269.7 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 177550 bytes 50095211 (50.0 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
# bring network interface up/down
sudo ifconfig eth0 up
sudo ifconfig eth0 down
iwconfigcheck if there are any wireless cards
iwconfig
lo no wireless extensions.
enp5s0 no wireless extensions.
eno1 no wireless extensions.
wlp6s0 IEEE 802.11 ESSID:off/any
Mode:Managed Access Point: Not-Associated
Retry short limit:7 RTS thr:off Fragment thr:off
Power Management:on
docker0 no wireless extensions.
hostname -I--all-ip-addresses all addresses for the host
192.168.1.55 192.168.2.39 172.17.0.1 172.16.8.1 240e:388:6252:300:7d55:a5e3:a0ad:7ce9 240e:388:6252:300:e5e7:1980:c300:527c
route
# Shows and manipulate IP routing table
route -n
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 192.168.1.1 0.0.0.0 UG 100 0 0 eno1
0.0.0.0 192.168.2.1 0.0.0.0 UG 600 0 0 wlp6s0
169.254.0.0 0.0.0.0 255.255.0.0 U 1000 0 0 wlp6s0
172.16.8.0 0.0.0.0 255.255.255.0 U 0 0 0 br-83bbca862df5
172.17.0.0 0.0.0.0 255.255.0.0 U 0 0 0 docker0
192.168.1.0 0.0.0.0 255.255.255.0 U 100 0 0 eno1
192.168.2.0 0.0.0.0 255.255.255.0 U 600 0 0 wlp6s0
192.168.2.0 192.168.2.1 255.255.255.0 UG 1500 0 0 wlp6s0
# similar to above
netstat -r -n
Kernel IP routing table
Destination Gateway Genmask Flags MSS Window irtt Iface
0.0.0.0 192.168.196.2 0.0.0.0 UG 0 0 0 ens33
169.254.0.0 0.0.0.0 255.255.0.0 U 0 0 0 ens33
192.168.196.0 0.0.0.0 255.255.255.0 U 0 0 0 ens33
route flags
- U: route is up
- H: target is a host
- G: use gateway
- R: reinstate route for dynamic routing
- D: dynamically installed by daemon or redirect
- M: modified from routing daemon or redirect
- A: installed by addrconf
- C: cache entry
!: reject route
ip route show
default via 192.168.71.1 dev eno1 proto dhcp src 192.168.71.113 metric 102
10.42.0.0/24 dev enp5s0 proto kernel scope link src 10.42.0.1 metric 103
172.17.0.0/16 dev docker0 proto kernel scope link src 172.17.0.1 linkdown
192.168.71.0/24 dev eno1 proto kernel scope link src 192.168.71.113 metric 102
sudo mii-tool eno1Check network cable
eno1: negotiated 1000baseT-FD flow-control, link ok
sudo dhclient -vquery local dhcp server
Internet Systems Consortium DHCP Client 4.4.1
Copyright 2004-2018 Internet Systems Consortium.
All rights reserved.
For info, please visit https://www.isc.org/software/dhcp/
Listening on LPF/veth102727a/8e:19:46:b9:1a:c1
Sending on LPF/veth102727a/8e:19:46:b9:1a:c1
Listening on LPF/vethf386f6e/c2:26:6d:c9:f6:3a
Sending on LPF/vethf386f6e/c2:26:6d:c9:f6:3a
Listening on LPF/vetha34c604/62:f7:ed:12:23:ea
Sending on LPF/vetha34c604/62:f7:ed:12:23:ea
Listening on LPF/veth08294be/e2:a3:3b:22:be:5d
Sending on LPF/veth08294be/e2:a3:3b:22:be:5d
Listening on LPF/veth1f8ce9e/5e:fc:40:cc:67:2c
Sending on LPF/veth1f8ce9e/5e:fc:40:cc:67:2c
Listening on LPF/veth7a5a49e/02:e1:a6:6a:49:e0
Sending on LPF/veth7a5a49e/02:e1:a6:6a:49:e0
Listening on LPF/veth70af89d/4e:f5:d7:94:ee:44
Sending on LPF/veth70af89d/4e:f5:d7:94:ee:44
Listening on LPF/veth8480f02/da:ba:e9:99:e3:53
Sending on LPF/veth8480f02/da:ba:e9:99:e3:53
Listening on LPF/vethde2cb61/ce:fa:77:51:34:cf
Sending on LPF/vethde2cb61/ce:fa:77:51:34:cf
Listening on LPF/veth81ac2a2/ce:95:33:51:ef:e9
Sending on LPF/veth81ac2a2/ce:95:33:51:ef:e9
Listening on LPF/vetha42c782/32:f7:93:df:7c:85
Sending on LPF/vetha42c782/32:f7:93:df:7c:85
Listening on LPF/veth90fb96a/7e:4f:be:e7:03:92
Sending on LPF/veth90fb96a/7e:4f:be:e7:03:92
Listening on LPF/veth67578e7/ba:7b:23:c4:41:5c
Sending on LPF/veth67578e7/ba:7b:23:c4:41:5c
Listening on LPF/br-83bbca862df5/02:42:49:e5:93:fc
Sending on LPF/br-83bbca862df5/02:42:49:e5:93:fc
Listening on LPF/docker0/02:42:cf:28:a7:14
Sending on LPF/docker0/02:42:cf:28:a7:14
Listening on LPF/wlp6s0/40:ec:99:48:94:82
Sending on LPF/wlp6s0/40:ec:99:48:94:82
Listening on LPF/eno1/54:b2:03:98:40:1e
Sending on LPF/eno1/54:b2:03:98:40:1e
Listening on LPF/enp5s0/54:b2:03:98:40:1f
Sending on LPF/enp5s0/54:b2:03:98:40:1f
Sending on Socket/fallback
DHCPDISCOVER on veth102727a to 255.255.255.255 port 67 interval 3 (xid=0xcd06230d)
DHCPDISCOVER on vethf386f6e to 255.255.255.255 port 67 interval 3 (xid=0x8a0ae250)
DHCPDISCOVER on vetha34c604 to 255.255.255.255 port 67 interval 3 (xid=0xa2e8942b)
DHCPDISCOVER on veth08294be to 255.255.255.255 port 67 interval 3 (xid=0x8f368c6d)
DHCPDISCOVER on veth1f8ce9e to 255.255.255.255 port 67 interval 3 (xid=0x47a6464f)
DHCPDISCOVER on veth7a5a49e to 255.255.255.255 port 67 interval 3 (xid=0xe63a7975)
DHCPDISCOVER on veth70af89d to 255.255.255.255 port 67 interval 3 (xid=0xbba91c00)
DHCPDISCOVER on veth8480f02 to 255.255.255.255 port 67 interval 3 (xid=0x53a54376)
DHCPDISCOVER on vethde2cb61 to 255.255.255.255 port 67 interval 3 (xid=0xcaba892e)
DHCPDISCOVER on veth81ac2a2 to 255.255.255.255 port 67 interval 3 (xid=0x42b1b08)
DHCPDISCOVER on vetha42c782 to 255.255.255.255 port 67 interval 3 (xid=0x23b1ef25)
DHCPDISCOVER on veth90fb96a to 255.255.255.255 port 67 interval 3 (xid=0x50e08e73)
DHCPDISCOVER on veth67578e7 to 255.255.255.255 port 67 interval 3 (xid=0x92652230)
DHCPDISCOVER on br-83bbca862df5 to 255.255.255.255 port 67 interval 3 (xid=0x56f1d800)
DHCPDISCOVER on docker0 to 255.255.255.255 port 67 interval 3 (xid=0xdf761c15)
DHCPDISCOVER on wlp6s0 to 255.255.255.255 port 67 interval 3 (xid=0x2ead5c6f)
DHCPDISCOVER on eno1 to 255.255.255.255 port 67 interval 3 (xid=0xf3f1ef7c)
DHCPDISCOVER on enp5s0 to 255.255.255.255 port 67 interval 3 (xid=0x68fd236b)
DHCPOFFER of 192.168.2.38 from 192.168.2.1
DHCPREQUEST for 192.168.2.38 on wlp6s0 to 255.255.255.255 port 67 (xid=0x6f5cad2e)
DHCPOFFER of 192.168.1.55 from 192.168.1.1
DHCPREQUEST for 192.168.1.55 on eno1 to 255.255.255.255 port 67 (xid=0x7ceff1f3)
DHCPACK of 192.168.2.38 from 192.168.2.1 (xid=0x2ead5c6f)
RTNETLINK answers: File exists
bound to 192.168.2.38 -- renewal in 40928 seconds.
arp
ARP cache entry state
| entry state | desc | action if used |
|---|---|---|
| permanent | never expires; never verified | reset use counter |
| noarp | normal expiration; never verified | reset use counter |
| reachable | normal expiration | reset use counter |
| stale | still usable; needs verification | reset use counter; change state to delay |
| delay | schedule ARP request; | needs verification reset use counter |
| probe | sending ARP request | reset use counter |
| incomplete | first ARP request | sent send ARP request |
| failed | no response received | send ARP request |
# View or add contents of the kernel's ARP table (RFC 826)
arp -a
_gateway (192.168.196.2) at 00:50:56:f2:2d:a9 [ether] on ens33
? (192.168.196.254) at 00:50:56:e7:72:8f [ether] on ens33
? (192.168.196.1) at 00:50:56:c0:00:08 [ether] on ens33
#
ip neighbor show
192.168.196.2 dev ens33 lladdr 00:50:56:f2:2d:a9 STALE
192.168.196.254 dev ens33 lladdr 00:50:56:e7:72:8f STALE
192.168.196.1 dev ens33 lladdr 00:50:56:c0:00:08 STALE
fe80::1767:ea8d:ae99:908c dev ens33 lladdr 00:50:56:c0:00:08 STALE
_gateway (192.168.2.1) at a0:de:0f:ad:87:2f [ether] on wlp6s0
? (172.16.8.6) at 02:42:ac:10:08:06 [ether] on br-83bbca862df5
? (172.16.8.53) at 02:42:ac:10:08:35 [ether] on br-83bbca862df5
? (172.16.8.150) at 02:42:ac:10:08:96 [ether] on br-83bbca862df5
? (172.16.8.61) at 02:42:ac:10:08:3d [ether] on br-83bbca862df5
? (192.168.1.4) at a0:de:0f:ad:31:30 [ether] on eno1
? (172.16.8.3) at 02:42:ac:10:08:03 [ether] on br-83bbca862df5
_gateway (192.168.1.1) at 14:e9:b2:37:b8:6f [ether] on eno1
netstat -plntuDisplay active service connection information
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:8031 0.0.0.0:* LISTEN 5358/docker-proxy
tcp 0 0 0.0.0.0:8000 0.0.0.0:* LISTEN 422579/node
tcp 0 0 0.0.0.0:8032 0.0.0.0:* LISTEN 5332/docker-proxy
tcp 0 0 0.0.0.0:8001 0.0.0.0:* LISTEN 422641/node
tcp 0 0 0.0.0.0:5601 0.0.0.0:* LISTEN 6042/docker-proxy
tcp 0 0 0.0.0.0:8033 0.0.0.0:* LISTEN 5282/docker-proxy
tcp 0 0 0.0.0.0:10022 0.0.0.0:* LISTEN 3964/docker-proxy
tcp 0 0 0.0.0.0:5672 0.0.0.0:* LISTEN 5268/docker-proxy
tcp 0 0 0.0.0.0:5000 0.0.0.0:* LISTEN 3869/docker-proxy
tcp 0 0 0.0.0.0:5001 0.0.0.0:* LISTEN 3855/docker-proxy
tcp 0 0 0.0.0.0:8043 0.0.0.0:* LISTEN 90658/docker-proxy
tcp 0 0 0.0.0.0:6379 0.0.0.0:* LISTEN 5508/docker-proxy
tcp 0 0 0.0.0.0:8045 0.0.0.0:* LISTEN 3951/docker-proxy
tcp 0 0 0.0.0.0:111 0.0.0.0:* LISTEN 1/init
tcp 0 0 0.0.0.0:9200 0.0.0.0:* LISTEN 5469/docker-proxy
tcp 0 0 0.0.0.0:9300 0.0.0.0:* LISTEN 5403/docker-proxy
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 923/systemd-resolve
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 1088/sshd: /usr/sbi
tcp 0 0 0.0.0.0:3000 0.0.0.0:* LISTEN 458176/node
tcp 0 0 0.0.0.0:15672 0.0.0.0:* LISTEN 5256/docker-proxy
tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 3935/docker-proxy
tcp6 0 0 :::111 :::* LISTEN 1/init
tcp6 0 0 :::22 :::* LISTEN 1088/sshd: /usr/sbi
udp 0 0 224.0.0.251:5353 0.0.0.0:* 7976/chrome --enabl
udp 0 0 224.0.0.251:5353 0.0.0.0:* 7976/chrome --enabl
udp 0 0 224.0.0.251:5353 0.0.0.0:* 7976/chrome --enabl
udp 0 0 0.0.0.0:5353 0.0.0.0:* 960/avahi-daemon: r
udp 0 0 127.0.0.53:53 0.0.0.0:* 923/systemd-resolve
udp 4352 0 0.0.0.0:68 0.0.0.0:* 1860/charon
udp 0 0 0.0.0.0:111 0.0.0.0:* 1/init
udp 0 0 0.0.0.0:32971 0.0.0.0:* 960/avahi-daemon: r
udp 0 0 0.0.0.0:500 0.0.0.0:* 1860/charon
udp 0 0 0.0.0.0:631 0.0.0.0:* 427816/cups-browsed
udp 0 0 0.0.0.0:35811 0.0.0.0:* 984/rsyslogd
udp 0 0 0.0.0.0:4500 0.0.0.0:* 1860/charon
udp6 0 0 :::5353 :::* 960/avahi-daemon: r
udp6 0 0 :::111 :::* 1/init
udp6 0 0 :::500 :::* 1860/charon
udp6 0 0 :::36855 :::* 960/avahi-daemon: r
udp6 0 0 :::4500 :::* 1860/charon
nslookup -type=any bing.comCheck IP Address linked to a domain name
Server: 127.0.0.53
Address: 127.0.0.53#53
Non-authoritative answer:
bing.com hinfo = "RFC8482" ""
Name: bing.com
Address: 204.79.197.200
Name: bing.com
Address: 13.107.21.200
bing.com nameserver = dns4.p09.nsone.net.
bing.com nameserver = dns2.p09.nsone.net.
bing.com nameserver = ns4-204.azure-dns.info.
bing.com nameserver = dns1.p09.nsone.net.
bing.com nameserver = ns3-204.azure-dns.org.
bing.com nameserver = ns1-204.azure-dns.com.
bing.com nameserver = dns3.p09.nsone.net.
bing.com nameserver = ns2-204.azure-dns.net.
dig bing.com -t anyQuery DNS related information
; <<>> DiG 9.16.1-Ubuntu <<>> bing.com -t any
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 54424
;; flags: qr rd ra; QUERY: 1, ANSWER: 9, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 65494
;; QUESTION SECTION:
;bing.com. IN ANY
;; ANSWER SECTION:
bing.com. 3270 IN HINFO "RFC8482" ""
bing.com. 139533 IN NS ns3-204.azure-dns.org.
bing.com. 139533 IN NS ns1-204.azure-dns.com.
bing.com. 139533 IN NS ns4-204.azure-dns.info.
bing.com. 139533 IN NS dns3.p09.nsone.net.
bing.com. 139533 IN NS dns2.p09.nsone.net.
bing.com. 139533 IN NS dns4.p09.nsone.net.
bing.com. 139533 IN NS dns1.p09.nsone.net.
bing.com. 139533 IN NS ns2-204.azure-dns.net.
;; Query time: 4 msec
;; SERVER: 127.0.0.53#53(127.0.0.53)
;; WHEN: Wed Jun 01 10:33:12 CST 2022
;; MSG SIZE rcvd: 282
systemd-resolve --status
Global
LLMNR setting: no
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
DNS Servers: 192.168.1.1
192.168.2.1
DNS Domain: ctc
DNSSEC NTA: 10.in-addr.arpa
16.172.in-addr.arpa
168.192.in-addr.arpa
17.172.in-addr.arpa
18.172.in-addr.arpa
19.172.in-addr.arpa
20.172.in-addr.arpa
21.172.in-addr.arpa
22.172.in-addr.arpa
23.172.in-addr.arpa
24.172.in-addr.arpa
25.172.in-addr.arpa
26.172.in-addr.arpa
27.172.in-addr.arpa
28.172.in-addr.arpa
29.172.in-addr.arpa
30.172.in-addr.arpa
31.172.in-addr.arpa
corp
d.f.ip6.arpa
home
internal
intranet
lan
local
private
test
Link 568 (veth102727a)
Current Scopes: none
DefaultRoute setting: no
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
Link 32 (vethf386f6e)
Current Scopes: none
DefaultRoute setting: no
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
Link 6 (br-83bbca862df5)
Current Scopes: none
DefaultRoute setting: no
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
Link 5 (docker0)
Current Scopes: none
DefaultRoute setting: no
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
Link 4 (wlp6s0)
Current Scopes: DNS
DefaultRoute setting: yes
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
DNS Servers: 192.168.2.1
DNS Domain: ~.
ctc
Link 3 (eno1)
Current Scopes: none
DefaultRoute setting: no
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
Link 2 (enp5s0)
Current Scopes: none
DefaultRoute setting: no
LLMNR setting: yes
MulticastDNS setting: no
DNSOverTLS setting: no
DNSSEC setting: no
DNSSEC supported: no
ping -c 6 bing.comTo check connectivity between two nodes
PING bing.com(2620:1ec:c11::200 (2620:1ec:c11::200)) 56 data bytes
64 bytes from 2620:1ec:c11::200 (2620:1ec:c11::200): icmp_seq=1 ttl=54 time=181 ms
64 bytes from 2620:1ec:c11::200 (2620:1ec:c11::200): icmp_seq=2 ttl=54 time=171 ms
64 bytes from 2620:1ec:c11::200 (2620:1ec:c11::200): icmp_seq=3 ttl=54 time=173 ms
64 bytes from 2620:1ec:c11::200 (2620:1ec:c11::200): icmp_seq=4 ttl=54 time=172 ms
64 bytes from 2620:1ec:c11::200 (2620:1ec:c11::200): icmp_seq=5 ttl=54 time=168 ms
64 bytes from 2620:1ec:c11::200 (2620:1ec:c11::200): icmp_seq=6 ttl=54 time=184 ms
--- bing.com ping statistics ---
6 packets transmitted, 6 received, 0% packet loss, time 6410ms
rtt min/avg/max/mdev = 168.047/174.720/183.562/5.510 ms
tracepath -b 188.166.16.132Similar to traceroute but doesn't require root privileges
1?: [LOCALHOST] pmtu 1500
1: _gateway (192.168.1.1) 0.488ms pmtu 1492
2: 1.95.21.222.dynamic.163.com (222.21.95.1) 8.452ms
3: 61.152.55.17 (61.152.55.17) 11.382ms
4: 101.95.120.102 (101.95.120.102) 7.438ms
5: 202.97.24.254 (202.97.24.254) 4.813ms asymm 6
6: no reply
7: 202.97.59.170 (202.97.59.170) 150.769ms
8: 218.30.54.245 (218.30.54.245) 165.961ms
9: no reply
10: ae-5.r25.asbnva02.us.bb.gin.ntt.net (129.250.3.188) 327.284ms asymm 11
11: if-ae-18-3.tcore2.l78-london.as6453.net (80.231.131.168) 261.551ms asymm 12
12: ae-3.a02.londen14.uk.bb.gin.ntt.net (129.250.3.191) 361.911ms asymm 11
13: if-ae-11-2.tcore1.ad1-amsterdam.as6453.net (80.231.152.26) 242.363ms asymm 9
14: 195.219.150.110 (195.219.150.110) 258.074ms asymm 11
15: 138.197.244.89 (138.197.244.89) 351.192ms asymm 11
16: 138.197.250.93 (138.197.250.93) 351.959ms asymm 12
17: no reply
18: no reply
19: 188.166.16.132 (188.166.16.132) 241.972ms reached
Resume: pmtu 1492 hops 19 back 15
nc -z -v -w 6 188.166.16.132 443
Connection to 188.166.16.132 443 port [tcp/https] succeeded!
openssl s_client -connect localhost:443
CONNECTED(00000003)
Can't use SSL_get_servername
depth=2 C = US, O = Internet Security Research Group, CN = ISRG Root X1
verify return:1
depth=1 C = US, O = Let's Encrypt, CN = R3
verify return:1
depth=0 CN = *.example.com
verify return:1
---
Certificate chain
0 s:CN = *.example.com
i:C = US, O = Let's Encrypt, CN = R3
1 s:C = US, O = Let's Encrypt, CN = R3
i:C = US, O = Internet Security Research Group, CN = ISRG Root X1
2 s:C = US, O = Internet Security Research Group, CN = ISRG Root X1
i:O = Digital Signature Trust Co., CN = DST Root CA X3
---
Server certificate
-----BEGIN CERTIFICATE-----
dPJlcdl29gEy8DDasaGjfHFBdcV+SBQ/COI=
-----END CERTIFICATE-----
subject=CN = *.example.com
issuer=C = US, O = Let's Encrypt, CN = R3
---
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: RSA-PSS
Server Temp Key: X25519, 253 bits
---
SSL handshake has read 4574 bytes and written 363 bytes
Verification: OK
---
curl -v -D - https://example.commtr -r -c 6 188.166.16.132Combines ping and tracepath into a single command
Start: 2022-06-01T11:55:31+0200
HOST: localhost Loss% Snt Last Avg Best Wrst StDev
1.|-- _gateway 0.0% 6 1.5 1.6 1.5 1.6 0.1
2.|-- _gateway 0.0% 6 2.7 3.3 2.5 6.1 1.4
3.|-- 1.95.21.222.broad.xw.sh.d 0.0% 6 7.1 9.7 6.6 13.5 2.6
4.|-- 61.152.55.17 0.0% 6 13.4 12.2 9.1 15.9 2.5
5.|-- 101.95.120.102 66.7% 6 6.9 8.2 6.9 9.5 1.8
6.|-- 202.97.57.157 50.0% 6 7.9 38.4 7.3 100.2 53.5
7.|-- 202.97.12.201 66.7% 6 7.4 7.8 7.4 8.2 0.5
8.|-- 202.97.59.170 0.0% 6 138.9 145.0 138.9 151.8 5.3
9.|-- 218.30.53.109 16.7% 6 267.2 269.6 252.6 305.0 20.8
10.|-- ??? 100.0 6 0.0 0.0 0.0 0.0 0.0
11.|-- ae-5.r25.asbnva02.us.bb.g 66.7% 6 318.4 316.5 314.5 318.4 2.7
12.|-- ae-7.r21.londen12.uk.bb.g 33.3% 6 361.2 360.3 352.2 365.6 5.7
13.|-- ae-3.a02.londen14.uk.bb.g 16.7% 6 358.3 356.3 350.0 359.4 3.8
14.|-- ae-1.a01.londen14.uk.bb.g 66.7% 6 353.5 353.1 352.7 353.5 0.6
15.|-- ae-1.digital-ocean.londen 50.0% 6 349.7 367.6 349.7 403.3 31.0
16.|-- 138.197.244.89 16.7% 6 443.3 373.2 353.8 443.3 39.2
17.|-- ??? 100.0 6 0.0 0.0 0.0 0.0 0.0
18.|-- ??? 100.0 6 0.0 0.0 0.0 0.0 0.0
19.|-- ??? 100.0 6 0.0 0.0 0.0 0.0 0.0
20.|-- ??? 100.0 6 0.0 0.0 0.0 0.0 0.0
21.|-- 188.166.16.132 16.7% 6 341.2 339.8 338.1 342.6 2.0
ss -t -aNetwork connection status
State Recv-Q Send-Q Local Address:Port Peer Address:Port Process
LISTEN 0 4096 0.0.0.0:8031 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:8032 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:5601 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:8033 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:10022 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:amqp 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:5000 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:5001 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:8043 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:6379 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:8045 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:sunrpc 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:9200 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:9300 0.0.0.0:*
LISTEN 0 4096 127.0.0.53%lo:domain 0.0.0.0:*
LISTEN 0 128 0.0.0.0:ssh 0.0.0.0:*
LISTEN 0 5 127.0.0.1:ipp 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:15672 0.0.0.0:*
LISTEN 0 4096 0.0.0.0:https 0.0.0.0:*
ESTAB 0 0 192.168.2.36:38002 180.163.150.34:https
ESTAB 0 0 192.168.2.36:46294 23.2.3.44:https
TIME-WAIT 0 0 192.168.2.36:59928 35.227.202.26:https
SYN-SENT 0 1 192.168.2.36:56418 185.84.60.29:https
FIN-WAIT-1 0 518 192.168.2.36:51034 23.207.173.39:https
ESTAB 0 0 192.168.2.36:53740 13.227.74.93:https
ESTAB 0 0 192.168.2.36:36202 69.173.158.64:https
SYN-SENT 0 1 192.168.2.36:38014 142.251.43.10:https
LAST-ACK 0 518 192.168.2.36:35356 35.190.60.146:https
SYN-SENT 0 1 192.168.2.36:56420 185.84.60.29:https
CLOSE-WAIT 32 0 192.168.2.36:39004 117.50.156.210:https
CLOSING 1 518 192.168.2.36:35358 35.190.60.146:https
ESTAB 0 0 192.168.2.36:56728 180.163.151.38:https
ESTAB 0 0 192.168.2.36:32912 50.16.30.16:https
ESTAB 0 0 192.168.2.36:46982 104.22.25.74:https
TIME-WAIT 0 0 192.168.2.36:32914 50.16.30.16:https
SYN-SENT 0 1 192.168.2.36:38010 142.251.43.10:https
SYN-SENT 0 1 192.168.2.36:34978 8.2.111.71:https
ESTAB 0 0 192.168.2.36:58166 209.167.231.15:https
ESTAB 0 0 192.168.2.36:60322 23.79.23.214:https
LISTEN 0 4096 [::]:sunrpc [::]:*
LISTEN 0 128 [::]:ssh [::]:*
tcpdump
: capturing and displaying packets src dst port
sudo tcpdump -Dlist all network interfaces
1.veth08294be [Up, Running]
2.wlp6s0 [Up, Running]
3.veth81ac2a2 [Up, Running]
4.veth8480f02 [Up, Running]
5.br-83bbca862df5 [Up, Running]
6.vethf386f6e [Up, Running]
7.veth67578e7 [Up, Running]
8.veth1f8ce9e [Up, Running]
9.veth7a5a49e [Up, Running]
10.vethde2cb61 [Up, Running]
11.veth70af89d [Up, Running]
12.veth90fb96a [Up, Running]
13.vetha34c604 [Up, Running]
14.vetha42c782 [Up, Running]
15.veth102727a [Up, Running]
16.lo [Up, Running, Loopback]
17.any (Pseudo-device that captures on all interfaces) [Up, Running]
18.enp5s0:avahi [Up]
19.enp5s0 [Up]
20.docker0 [Up]
21.eno1 [Up]
22.bluetooth-monitor (Bluetooth Linux Monitor) [none]
23.nflog (Linux netfilter log (NFLOG) interface) [none]
24.nfqueue (Linux netfilter queue (NFQUEUE) interface) [none]
25.bluetooth0 (Bluetooth adapter number 0) [none]
sudo tcpdump -i wlp6s0 -c 10 host 180.163.151.33Capture traffic to and from one host
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on wlp6s0, link-type EN10MB (Ethernet), capture size 262144 bytes
13:58:47.973830 IP localhost.47230 > 180.163.151.33.https: Flags [P.], seq 4003020267:4003020331, ack 1902087721, win 501, options [nop,nop,TS val 951179288 ecr 489958243], length 64
13:58:47.974251 IP localhost.47230 > 180.163.151.33.https: Flags [P.], seq 64:103, ack 1, win 501, options [nop,nop,TS val 951179289 ecr 489958243], length 39
13:58:47.989193 IP 180.163.151.33.https > localhost.47230: Flags [.], ack 64, win 271, options [nop,nop,TS val 489971947 ecr 951179288], length 0
13:58:47.989501 IP 180.163.151.33.https > localhost.47230: Flags [.], ack 103, win 271, options [nop,nop,TS val 489971947 ecr 951179289], length 0
13:58:48.019337 IP 180.163.151.33.https > localhost.47230: Flags [P.], seq 1:92, ack 103, win 271, options [nop,nop,TS val 489971977 ecr 951179289], length 91
13:58:48.020751 IP 180.163.151.33.https > localhost.47230: Flags [P.], seq 92:2910, ack 103, win 271, options [nop,nop,TS val 489971977 ecr 951179289], length 2818
13:58:48.020803 IP localhost.47230 > 180.163.151.33.https: Flags [.], ack 2910, win 501, options [nop,nop,TS val 951179335 ecr 489971977], length 0
13:58:48.021150 IP 180.163.151.33.https > localhost.47230: Flags [P.], seq 2910:4319, ack 103, win 271, options [nop,nop,TS val 489971978 ecr 951179289], length 1409
13:58:48.021208 IP localhost.47230 > 180.163.151.33.https: Flags [.], ack 4319, win 501, options [nop,nop,TS val 951179336 ecr 489971978], length 0
13:58:48.022234 IP 180.163.151.33.https > localhost.47230: Flags [.], seq 4319:7119, ack 103, win 271, options [nop,nop,TS val 489971978 ecr 951179289], length 2800
10 packets captured
11 packets received by filter
0 packets dropped by kernel
sudo tcpdump -i br-83bbca862df5 net 172.16.8.0/24Capture traffic to and from a network
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on br-83bbca862df5, link-type EN10MB (Ethernet), capture size 262144 bytes
14:09:57.097639 IP 172.16.8.8.27017 > 172.16.8.6.44674: Flags [P.], seq 2064386111:2064386623, ack 145516422, win 9855, options [nop,nop,TS val 220809160 ecr 4054206566], length 512
14:09:57.097640 IP 172.16.8.8.27017 > 172.16.8.7.37246: Flags [P.], seq 2486215900:2486216414, ack 299050389, win 9867, options [nop,nop,TS val 1083927827 ecr 1985851862], length 514
14:09:57.097727 IP 172.16.8.7.37246 > 172.16.8.8.27017: Flags [.], ack 514, win 9773, options [nop,nop,TS val 1985856859 ecr 1083927827], length 0
14:09:57.100281 IP 172.16.8.6.44674 > 172.16.8.8.27017: Flags [P.], seq 1:478, ack 512, win 9797, options [nop,nop,TS val 4054211566 ecr 220809160], length 477
14:09:57.100347 IP 172.16.8.7.37246 > 172.16.8.8.27017: Flags [P.], seq 1:466, ack 514, win 9773, options [nop,nop,TS val 1985856862 ecr 1083927827], length 465
14:09:57.100349 IP 172.16.8.8.27017 > 172.16.8.6.44674: Flags [.], ack 478, win 9855, options [nop,nop,TS val 220809163 ecr 4054211566], length 0
14:09:57.100409 IP 172.16.8.8.27017 > 172.16.8.7.37246: Flags [.], ack 466, win 9867, options [nop,nop,TS val 1083927830 ecr 1985856862], length 0
14:09:57.100410 IP 172.16.8.6.44676 > 172.16.8.8.27017: Flags [P.], seq 3072520060:3072520408, ack 1504804212, win 9855, options [nop,nop,TS val 4054211566 ecr 220804162], length 348
14:09:57.100424 IP 172.16.8.7.37244 > 172.16.8.8.27017: Flags [P.], seq 2397327365:2397327713, ack 3338518484, win 9797, options [nop,nop,TS val 1985856862 ecr 1083922829], length 348
14:10:16.065454 IP 172.16.8.51.9200 > 172.16.8.53.47878: Flags [P.], seq 315:629, ack 8030, win 501, options [nop,nop,TS val 3728242482 ecr 2885212531], length 314
14:10:16.065488 IP 172.16.8.53.47878 > 172.16.8.51.9200: Flags [.], ack 629, win 2267, options [nop,nop,TS val 2885212535 ecr 3728242482], length 0
14:10:16.578428 IP 172.16.8.150.43282 > 172.16.8.51.9200: Flags [.], ack 1, win 569, options [nop,nop,TS val 1430857085 ecr 3551814464], length 0
14:10:16.578446 IP 172.16.8.51.9200 > 172.16.8.150.43282: Flags [.], ack 1, win 501, options [nop,nop,TS val 3551815492 ecr 1424336409], length 0
^C
214 packets captured
1193 packets received by filter
948 packets dropped by kernel
nmcli
# Usuage: `nmcli [OPTIONS] OBJECT { COMMAND | help }`
# listing available connections on the system
nmcli c show
NAME UUID TYPE DEVICE
eth1 10a92e55-4c60-496e-9b9e-7a4ec8e75d94 ethernet enp5s0
eth0 ecf5c09f-6d42-4045-b12d-22ab846ddfb9 ethernet eno1
lo 18eac107-07f1-401b-9440-4a3c1086cebf loopback lo
docker0 24bd60c3-faa1-4413-9964-b46ceb373ff7 bridge docker0
nmap
# Scan a Single Host
nmap 192.168.1.13
Starting Nmap 7.01 ( https://nmap.org ) at 2022-05-23 13:44 CST
Nmap scan report for 192.168.1.13 (192.168.1.13)
Host is up (0.013s latency).
Not shown: 996 filtered ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Nmap done: 1 IP address (1 host up) scanned in 9.04 seconds
# Scan Multiple Hosts
nmap 192.168.1.0/24
# Scan a Range of Ports:
nmap -p 1-100 192.168.1.1
Starting Nmap 7.01 ( https://nmap.org ) at 2022-05-23 13:53 CST
Nmap scan report for 192.168.1.14 (192.168.1.14)
Host is up (0.0039s latency).
Not shown: 996 filtered ports
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Nmap done: 1 IP address (1 host up) scanned in 5.70 seconds
# Scan for OS Detection
nmap -O 192.168.1.1
Nmap scan report for 192.168.1.1 (192.168.1.1)
Host is up (0.00089s latency).
Not shown: 994 filtered ports
PORT STATE SERVICE
80/tcp open http
139/tcp open netbios-ssn
443/tcp open https
445/tcp open microsoft-ds
5080/tcp open onscreen
8080/tcp open http-proxy
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: WAP
Running: Actiontec embedded, Linux
OS CPE: cpe:/h:actiontec:mi424wr-gen3i cpe:/o:linux:linux_kernel
OS details: Actiontec MI424WR-GEN3I WAP
OS detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 44.49 seconds
# Scan for Service Version Detection
nmap -sV 192.168.1.1
Nmap scan report for 192.168.1.1 (192.168.1.1)
Host is up (0.0037s latency).
Not shown: 994 filtered ports
PORT STATE SERVICE VERSION
80/tcp open http
139/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
443/tcp open tcpwrapped
445/tcp open netbios-ssn Samba smbd 3.X (workgroup: WORKGROUP)
5080/tcp open onscreen?
8080/tcp open http-proxy
3 services unrecognized despite returning data. If you know the service/version, please submit the following fingerprints at https://nmap.org/cgi-bin/submit.cgi?new-service :
==============NEXT SERVICE FINGERPRINT (SUBMIT INDIVIDUALLY)==============
SF-Port80-TCP:V=7.01%I=7%D=5/23%Time=664F6784%P=x86_64-pc-linux-gnu%r(GetR
SF:equest,2273,"HTTP/1\.0\x20200\x20OK\r\nServer:\x20\r\nContent-Type:\x20
SF:text/html;\x20charset=gb2312\r\nAccept-Ranges:\x20bytes\r\nConnection:\
SF:x20close\r\nCache-Control:\x20no-cache,no-store\r\nExpires:\x200\r\nCon
SF:tent-Length:\x208430\r\nSet-Cookie:\x20_TESTCOOKIEHTTP=1;\x20PATH=/;\x2
SF:0HttpOnly;\x20SameSite=Strict\r\nX-Frame-Options:\x20SAMEORIGIN\r\nX-Co
SF:ntent-Type-Options:\x20nosniff\r\nX-XSS-Protection:\x201;\x20mode=block
SF:\r\nContent-Security-Policy:\x20frame-ancestors\x20'self'\r\n\r\n\n\n\n
SF:\n\n\n\n\n
# Scan for Common Ports
nmap -F 192.168.1.1
# Scan for Specific Hostnames
nmap -sL 192.168.1.0/24
IPTABLES
- Syntax: iptables [-t table] command [match] [target/jump]
- Table: nat/mangle/filter/raw
- Commands:
| Command | Example | Explanation |
|---|---|---|
| -A, --append | iptables -A INPUT ... | [1]# |
| -D, --delete | iptables -D INPUT --dport 80 -j DROP, iptables -D INPUT 1 | [2]# |
| -R, --replace | iptables -R INPUT 1 -s 192.168.0.1 -j DROP | [3]# |
| -I, --insert | iptables -I INPUT 1 --dport 80 -j ACCEPT | [4]# |
| -L, --list | iptables -L INPUT | [5]# |
| -F, --flush | iptables -F INPUT | [6]# |
| -N, --new-chain | iptables -N allowed | [7]# |
| -X, --delete-chain | iptables -X allowed | [8]# |
Example Explanation:
- This command appends the rule to the end of the chain
- This command deletes a rule in a chain. This could be done in two ways; either by entering the whole rule to match (as in the first example), or by specifying the rule number that you want to match
- This command replaces the old entry at the specified line. It works in the same way as the --delete command, but instead of totally deleting the entry, it will replace it with a new entry.
- Insert a rule somewhere in a chain. The rule is inserted as the actual number that we specify.
- This command lists all the entries in the specified chain
- This command flushes all rules from the specified chain and is equivalent to deleting each rule one by one, but is quite a bit faster. The command can be used without options, and will then delete all rules in all chains within the specified table.
- This command tells the kernel to create a new chain of the specified name in the specified table. In the above example we create a chain called allowed. Note that there must not already be a chain or target of the same name.
- This command deletes the specified chain from the table. For this command to work, there must be no rules that refer to the chain that is to be deleted. In other words, you would have to replace or delete all rules referring to the chain before actually deleting the chain. If this command is used without any options, all chains but those built in to the specified table will be deleted.
- Options
- Matches:
- Implicit matches: TCP/UDP/ICMP/SCTP
- Explicit matches: Addrtype/Conntrack/Dscp/Ecn/Hashlimit/IP range/Mac/Packet type/Realm/State/Tcpmss/Tos/Ttl/Unclean
- Targets & jumps: ACCEPT/CLASSIFY/CLUSTERIP/CONNMARK/DNAT/DROP/DSCP/ECN/LOG/MASQUERADE/NETMAP/NFQUEUE/NOTRACK/QUEUE/REDIRECT/REJECT/RETURN/SAME/SECMARK/SNAT/TCPMSS/TOS/TTL/ULOG
# enable forwarding (NAT)
echo "1" > /proc/sys/net/ipv4/ip_forward
# verify forwarding (NAT)
sudo sysctl net.ipv4.ip_forward
# lists your current rules in iptables
sudo iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHED
ACCEPT tcp -- anywhere anywhere tcp dpt:ssh
ACCEPT tcp -- anywhere anywhere tcp dpt:www
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
# list iptables in grater detail
sudo iptables -v -x -n -L
# the following commands redirect all traffic from enp5s0 to eno1 back and forth
sudo ip addr add 10.42.0.0/24 dev enp5s0
# Enabling SNAT (MASQUERADE) functionality on eno1
sudo iptables -t nat -A POSTROUTING -o eno1 -j MASQUERADE
# FWD: Allow all connections OUT and only existing and related ones IN
sudo iptables -A FORWARD -m conntrack --ctstate RELATED,ESTABLISHED -j ACCEPT
sudo iptables -A FORWARD -i enp5s0 -o eno1 -j ACCEPT
other system info commands
| commands | description |
|---|---|
| dmesg | Kernel Buffer |
| vmstat | virtual memory |
| pidstat | checks every pid status |
| mtr | checks network latency |
| mpstat | checks every CPU usages |
| iostat | checks disk status |
| free | checks memory status |
| sar | checks complete system activity |
| ss | Checks connection performance |
| iftop | Check network performance |
| smem | Checks memory allocated to per process |
| iperf | to measure the bandwidth and the quality of a network link |
Page Source